From Minecraft to Deutsche Telekom - Cyberthrowback Mirai
“In the dystopian future of 2030, the Japanese government is cracking down on any perceived immoral activity from using risqué language to distributing lewd materials in the country, to the point where all citizens are forced to wear high-tech devices called Peace Makers (PM) at all times that analyze every spoken word and hand motions for any action that could break the law. A new high school student named Tanukichi Okuma enters the country’s leading elite ‘public morals school’ to reunite with his crush and student council president, Anna Nishikinomiya.” (Wikipedia)
Wait a minute. What?
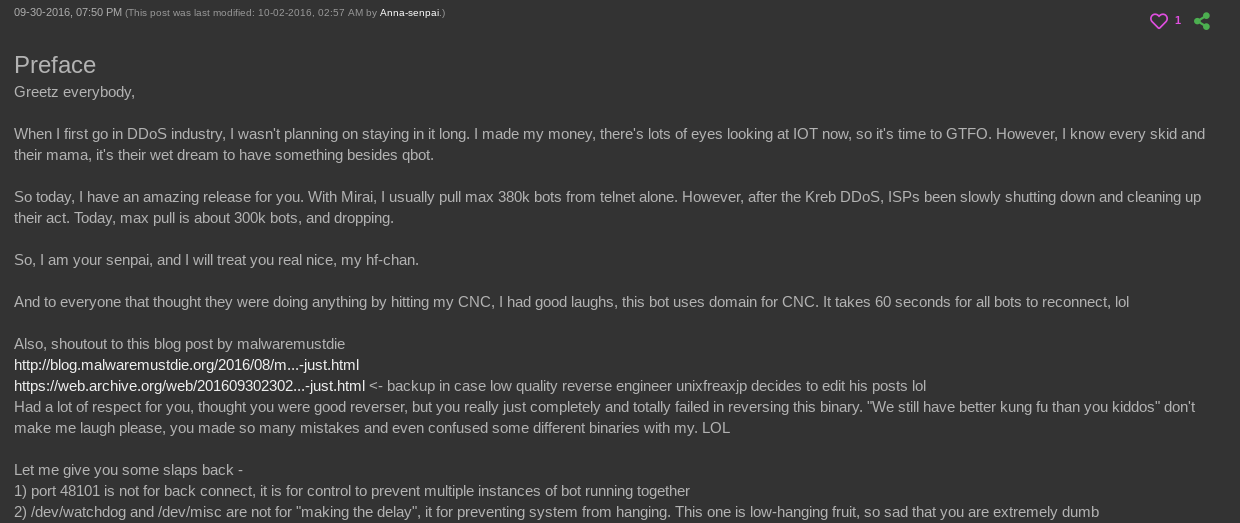
This is the description of the manga “Shimoneta: A Boring World Where the Concept of Dirty Jokes Doesn’t Exist”. This dystopian manga series apparently inspired hackers in the real world as well, with a user named “Anna-senpai” and matching profile picture (Anna Nishikinomiya) posting the source code of the Mirai botnet on a hacker forum in 2016.

Mirai was probably originally developed to cripple Minecraft servers and was subsequently used in other attacks, such as the November 2016 attack on around one million german Telekom Speedport routers.
In this so-called DDoS (Distributed Denial of Service) attack, infected and controlled IoT (Internet of Things) devices, such as routers, refrigerators, or surveillance cameras, were used to overload systems with requests and thus paralyze them.
But let’s start from the beginning.
We are sometime in 2014 to 2016, Minecraft had just been purchased by Microsoft and was at the peak of its popularity and player numbers. The high popularity, boosted by streaming platforms and the emerging Let’s Play scene, as well as the huge media hype around Minecraft made the initial non-commercial fan and private servers now a real source of money. A popular Minecraft server was now worth cash and could be monetized, at least as long as it was accessible and the players did not stay away from it.
It was probably during this time that three young American college students came up with the idea to get more users for their own Minecraft server by crippling other competitors with DDoS attacks and making them unusable. To carry out these attacks on a really large scale, the three set up a botnet of hundreds of thousands of infected machines. This is pressumably how the Mirai botnet was born.

In order to gain control over these primarily poorly protected IoT devices, a two-pronged approach was taken. On the one hand, known but previously unpatched vulnerabilities were exploited, and on the other hand, preset default logins were used. The following is a small excerpt from these default logins:
root admin
admin admin
root 888888
root xmhdipc
root default
root 123456
root 54321
support support
root (none)
admin password
root root
root 12345
user user
admin (none)
root pass
admin admin1234
root 1111
admin smcadmin
Administrator admin
service service
supervisor supervisor
tech tech
Since DDoS attacks on Minecraft servers were not uncommon at that time, several commercial DDoS protection offers emerged, such as from the French telecommunications provider OVH. This was also one of the first real big targets of Mirai. In the fall of 2016, one of the largest DDoS attacks ever occurred, mainly executed via infected “smart cameras”. Other targets were also attacked, such as the DNS Service Provider Dyn, whose outage even temporarily affected the accessibility of Twitter, Reddit and other well-known websites.
While these attacks were still ongoing, a user named “Anna-senpai” (based on Shimoneta) then published the source code for controlling a botnet for DDoS attacks in a hacker forum, for which the name Mirai was first used.
In the wake of the attacks that took place and the obvious vulnerability of even major telecommunications providers, greater media attention arose, naturally coupled with questions about the motives and the actors behind these actions. The following quote from wired reflects the mood of many expert voices at the time: “Someone has been probing the defenses of the companies that run critical pieces of the internet. These probes take the form of precisely calibrated attacks designed to determine exactly how well these companies can defend themselves, and what would be required to take them down,” wrote security expert Bruce Schneier in September 2016. “We don’t know who is doing this, but it feels like a large nation-state. China or Russia would be my first guesses.” Source.
Meanwhile, in reality, the real brains behind Mirai discuss the incompetence of malware analysts in the 36-page forum discussion that unfolded from the release of their source code. Other topics of the discussion, which splits into different strands, are the relationship between Mirai and the anime “Future diary - Mirai Nikki” or the fact that in Mirai’s source code, when logging in to a Command and Control Server the message “я люблю куриные наггетсы” is displayed, which presumably means something like “I love Chicken Nuggets”.

Once Mirai was known and the source code was accessible, it could be used by others for further attacks and to build their own botnets. This is how the attack on German Telekom’s Speedport routers in November 2016 was based on Mirai. Although this failed in its goal of adding the routers to the botnet, the attack caused them to crash, completely cutting off around one million German Telekom customers from the network. Quote from the Tagesspiegel on the incident:
“Security experts repeatedly refer to the machinations of Russian groups. […] The intelligence service had indications of ‘preparatory actions’ for attacks by Sofacy. The group has been active since 2007 and is increasingly used against states in the West. Security circles speak of Russian retaliation for the sanctions imposed on the country.”(Source Tagesspiegel).
In fact, however, behind the attack was an only moderately technically skilled dude from the UK, who claimed responsibility for the attack, as Der Spiegel later reported. Apparently out of financial interest and on behalf of a telecommunications provider from liberia, he had tried to set up his own botnet in order to sabotage competing providers.
Then, in December 2018, the full story of how the original Mirai network came to be was revealed: Before an American court, the three college students pleaded guilty and made comprehensive confessions. This was preceded by investigations by the FBI.
The story of Mirai shows impressively that events in the hacker scene and their backgrounds are much more complex than some would assume. Almost like in a good hacker movie, many things are not what they seem at first glance. This is particularly evident in the case of Mirai: It wasn’t nation states that were gearing up for global cyberwar, but a Minecraft scam developed by three American teenagers that paralyzed the infrastructure of well-known telecommunications providers in one fell swoop. The consequences to be drawn from this episode, on the other hand, are clear and unambiguous: danger always threatens when half-baked IT security solutions are used, and even worse when the basic rules of security are completely ignored, as in the case of many camera manufacturers, who set their logins unchangeably to “admin” with the password “admin”. And these resulting dangers extend far beyond the individual devices.
One of the brains behind Mirai now works for the FBI, apparently he is still a big anime fan.